ODAC Zero-Config Deployments

Developers spend more time writing Dockerfiles, tweaking YAML manifests, and debugging reverse proxy headers than writing actual business logic. The modern deployment pipeline has devolved into a brittle, multi-layered Rube Goldberg machine. We wanted a system where pushing code actually meant deploying code, without the tax of configuration files.
That is why ODAC utilizes a strict zero-config deployment architecture. We stripped away the need for external dependency management and built an orchestration engine that inherently understands what your application needs to run.
Architectural Intelligence over Manual Configuration
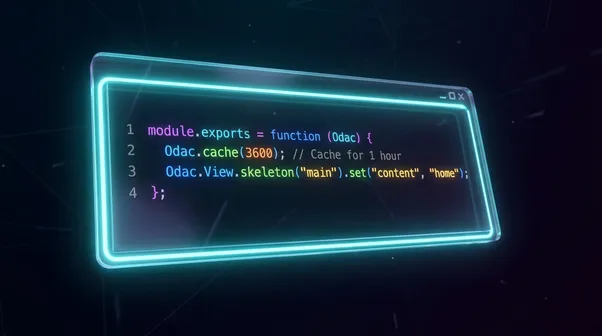
When you execute an odac deployment command, the platform does not ask you for a build context or a port mapping. Instead, the orchestrator inspects the source code and makes deterministic decisions.
At the core of this is the SCRIPT_RUNNERS mapping within the ODAC orchestration layer. By analyzing the structural composition of the repository, ODAC automatically assigns the correct, hardened Alpine Linux image. Whether it detects Python files requiring python:alpine or JavaScript files needing node:lts-alpine, the platform provisions the exact minimal runtime environment required.
This means absolute zero boilerplate:
- No
Dockerfilerequired: The orchestration engine infers your stack automatically based on file extensions. - No custom build scripts: Container environments are provisioned on demand.
- No port binding chaos: Application ports are auto-detected via image
EXPOSEmetadata or advanced HTTP probing.
Build Isolation and Determinism
A major bottleneck in automated deployments is state corruption during concurrent pushes. Traditional CI/CD pipelines often stumble over parallel builds, leading to orphaned containers or locked directories.
To solve this, the ODAC container orchestration module implements a strict build locking mechanism. When a deployment is triggered, the system acquires an application-level lock, guaranteeing that rapid, successive code pushes cannot trigger overlapping build tasks.
Furthermore, we eliminated timestamps in favor of deterministic Runtime IDs. Every container, build artifact, and process is tagged with a unique, cryptographically secure identifier. This absolutely eradicates naming collisions and ensures predictable container lifecycles.
Secure Sourcing and Blue/Green Rollouts
Fetching the code itself requires absolute security. Instead of relying on host-level git binaries, ODAC utilizes an isolated alpine/git container to perform repository clones.
We engineered multiple layers of defense and visibility during the build phase:
- Isolated Git Operations: Repositories are cloned inside an ephemeral container.
- Injection Prevention: We explicitly pass Git branches as Docker environment variables to completely neutralize any risk of shell injection attacks.
- Real-Time Git Logs: Our build system streams live logs with advanced noise filtering for absolute deployment visibility.
Once the application is built and running in its isolated container, the deployment is not simply marked complete. Native Blue/Green deployments occur at the infrastructure level.
Before a single byte of production traffic is routed to the newly deployed container, ODAC's internal load balancer executes rigorous HTTP health checks. Only when the new instance proves it is fully responsive on its designated port does the traffic switch over—guaranteeing true Enterprise-Grade Zero-Downtime.
The Result: Pure Engineering Velocity
By absorbing the complexity of building, port-binding, and reverse proxying, ODAC lets developers return to their primary objective: engineering software. You push the code. ODAC handles the infrastructure.