Secure Container Isolation in ODAC
The traditional shared hosting model is fundamentally broken. When you colocate multiple applications on a single operating system without strict boundaries, you aren't just sharing resources—you are sharing vulnerabilities, memory leaks, and CPU spikes. For years, the industry accepted the "noisy neighbor" problem as an unavoidable tax on server density. We refused to pay it.
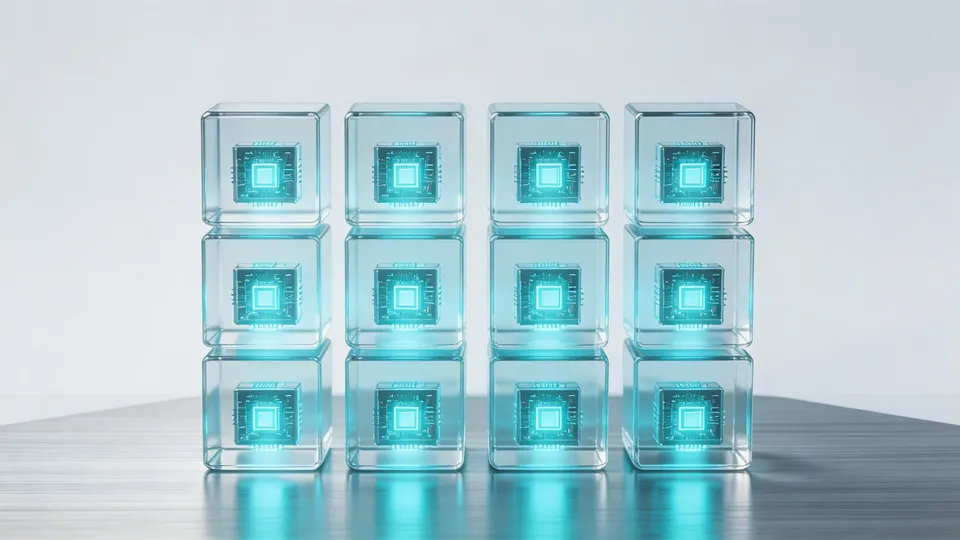
With ODAC, we engineered the platform around a singular philosophy: your deployment is an island. By provisioning every application into isolated, lightweight containers, ODAC guarantees absolute resource determinism. This isn't just about keeping things tidy; it is about ensuring that a rogue background job in one service cannot mathematically impact the latency of another.
The Anatomy of a Noisy Neighbor
In a standard naked deployment, processes fight a zero-sum war for the host's kernel scheduler. A poorly optimized script suddenly hoarding memory will trigger the out-of-memory (OOM) killer, which often arbitrarily targets the heaviest process. Suddenly, your mission-critical API drops offline because a forgotten internal dashboard decided to parse a massive JSON file.
We analyzed these failure modes deeply. The solution wasn't to throw more hardware at the problem, nor was it to implement brittle, user-space monitoring scripts. The only architectural guarantee against systemic degradation is strict, kernel-level process isolation.
Engineered for Absolute Isolation
ODAC automatically wraps every deployed service in its own immutable container boundary. There is no configuration required; the orchestration is entirely transparent to the developer. When you deploy an application, the ODAC orchestrator locks it into a deterministic environment.
Here is how our isolation architecture changes the game for self-hosted platforms:
- Strict Hardware Fencing: Each container is allocated precise boundaries. CPU cycles and memory limits are enforced at the virtualization layer, meaning an application can only ever crash itself.
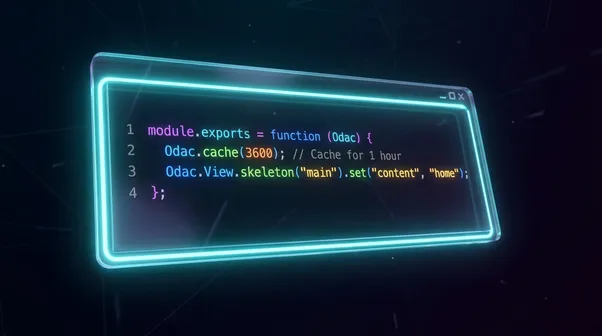
- Network Segregation: Applications are provisioned into a dedicated bridge network (
odac-network). The ODAC high-performance Go proxy routes traffic directly from the edge to the container's isolated internal port (typically Port 1071), entirely bypassing the host's exposed port bindings. - Deterministic Runtime IDs: Under the hood, ODAC abandons fragile timestamp-based naming. We utilize deterministic Runtime ID generation to prevent naming collisions, ensuring that our internal Docker management service can perfectly map and lifecycle every isolated instance.
- Socket-Level Communication: We mount the ODAC API socket directly into the container as a read-only volume (
/odac:ro). This establishes a secure, zero-overhead communication channel between the application and the host orchestrator without exposing unnecessary network ports.
Deploying the Fortress
The beauty of this architecture is its invisibility. You do not need to write complex orchestration manifests or manage Docker networks manually. You simply push your code.
# Provisioning a securely isolated application
odac app create
In milliseconds, ODAC handles the dependency mapping, pulls the correct Alpine-based runtime image, and locks the application inside its isolated vault. The result is a self-hosted cloud that feels as robust as bare metal, but operates with the agility of serverless.
By eliminating the noisy neighbor constraint, ODAC allows you to confidently push your hardware to its absolute limit. Total isolation, zero configuration, and enterprise-grade peace of mind.