ODAC.JS Enhanced Auth Token Metadata
Security is often treated as a binary state: a user is either logged in or they are not. In the enterprise world, knowing that a user is authenticated is only half the battle. Knowing the provenance of that session (the originating IP address and the precise moment of creation) is what separates a simple side project from a robust, auditable system.
We built ODAC.JS to eliminate the boilerplate that slows down high-performance teams. Today, we are making session auditing as effortless as a single method call with the introduction of the enhanced Odac.Auth.token() API.
The Why: Moving Beyond Binary Auth
Previously, if you wanted to build a "Security Activity" log or verify if a user's session originated from a suspicious IP address, you had to drop down to the database layer. You would manually query the token table, match the current session ID, and parse the metadata.
It worked, but it was friction. At ODAC.JS, we believe that if the framework stores the data, the framework should provide a clean, high-level way to access it. The new Odac.Auth.token() method provides direct access to the underlying session record without you ever writing a single WHERE clause.
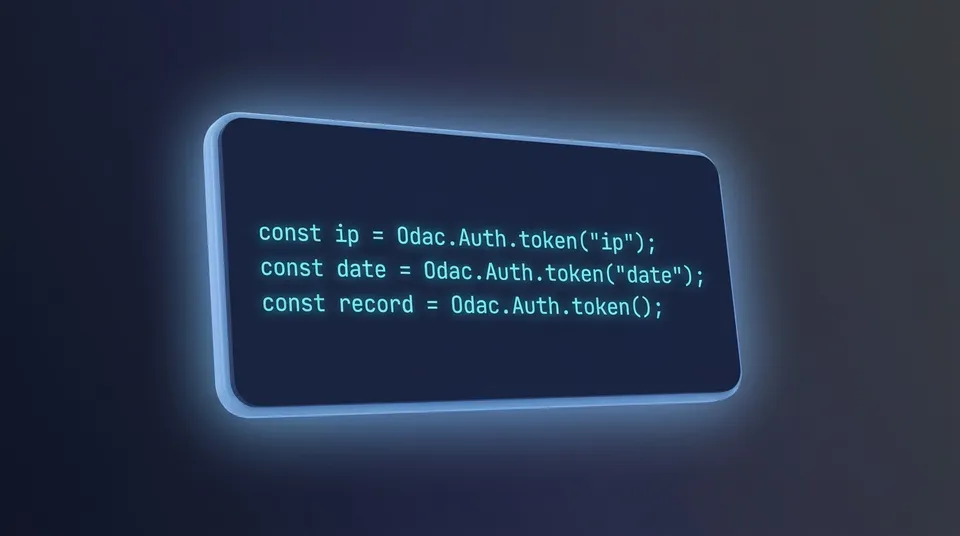
Show Me The Code
Accessing session metadata is now a first-class citizen in your controllers. Whether you need the full record or a specific column, the API remains intuitive and dry.
// Quick access to session metadata in a controller
module.exports = async function (Odac) {
if (!await Odac.Auth.check()) {
return Odac.direct('/login')
}
// Retrieve specific metadata fields
const sessionIp = Odac.Auth.token('ip')
const sessionDate = Odac.Auth.token('date')
return `Last login from ${sessionIp} on ${sessionDate}`
}
Real-World Scenario: Security Auditing
Imagine you are building a dashboard that alerts users when a new device logs into their account. Instead of complex joins, you can now pipe this data directly into your views or logging services.
// A security audit controller
module.exports = async function (Odac) {
await Odac.Auth.check()
const tokenData = {
ip: Odac.Auth.token('ip'),
created_at: Odac.Auth.token('date'),
session_id: Odac.Auth.token('id')
}
// Log the access to your audit table
await Odac.DB.security_logs.insert({
user_id: Odac.Auth.user('id'),
...tokenData,
event: 'dashboard_access'
})
// Set up the view parts
Odac.View.set({
skeleton: 'main',
header: 'main',
content: 'security.logs',
footer: 'main'
})
}
Handling Session States
One critical detail for developers: the Odac.Auth.token() method is context-aware. If no active session is detected, the method returns false. This design encourages defensive programming and ensures your application handles guest states gracefully.
// Defensive check for session data
const ipAddress = Odac.Auth.token('ip')
if (ipAddress === false) {
// Handle unauthenticated state or guest access
console.log('No active session found')
} else {
// Proceed with session-specific logic
console.log(`Current session IP: ${ipAddress}`)
}
Performance and Precision
Like every feature in ODAC.JS, the token API is optimized for speed. Since the authentication record is already retrieved during the Odac.Auth.check() lifecycle, calling token() incurs zero additional database overhead. It is a pure, O(1) retrieval from the framework's internal state.
This update is part of our ongoing commitment to making ODAC.JS the most developer-friendly, "Enterprise-Grade" framework in the Node.js ecosystem. By exposing these granular details through a clean abstraction, we enable you to build more secure, transparent applications in a fraction of the time.