Engineering the Zero-Bloat Cloud

Modern software development has a dependency problem. The industry has conditioned us to npm install our way out of every minor inconvenience, leading to a "bloat-first" mentality that sacrifices security and performance for convenience.
At ODAC, we decided to take a different path.
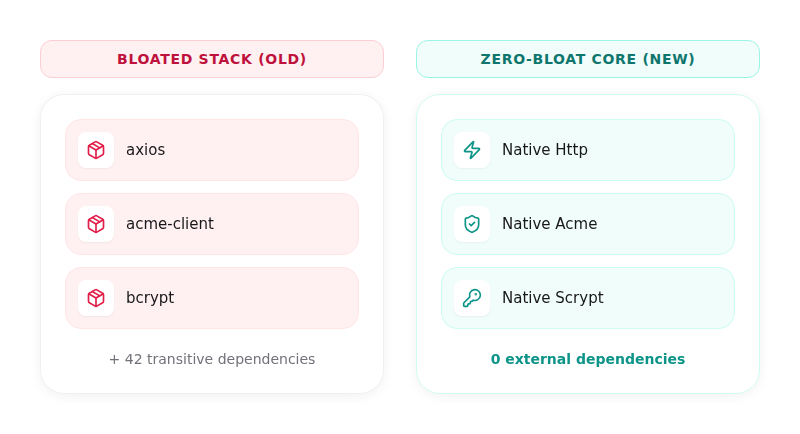
We are proud to announce the completion of our transition to a Zero-Bloat Architecture. By stripping away heavy external dependencies like axios, acme-client, and bcrypt, we have rebuilt the ODAC core to run entirely on native, high-performance Node.js modules.
This is not just about reducing our node_modules folder size. It is about architectural purity, deterministic security, and extreme performance.
The Cost of Convenience
Every external dependency is a liability. It is a potential entry point for a supply chain attack, a black box that adds milliseconds to execution time, and a memory hog that eats into your server's resources.
When you are building a self-hosted cloud platform designed to manage mission-critical infrastructure, "good enough" is a failure. We audited our core agent and found that the industry-standard libraries we were using were carrying too much baggage.
We did not need a generic HTTP client with a thousand features we would never use. We needed a razor-sharp, enterprise-grade client optimized for our specific orchestration needs.
Introducing the Native HTTP Core
The first to go was axios. While it is a fantastic library for general web development, it adds unnecessary overhead for a server-side orchestrator.
Our new native Http core is a zero-dependency implementation built directly on the Node.js http and https modules. It supports standard TCP and Unix Domain Sockets natively, providing the high-throughput, low-latency communication required for the ODAC orchestrator to talk to its high-performance Go proxies and background services.
By moving to a native implementation, we eliminated the overhead of generic interceptors and complex configuration objects. The result is a faster, more predictable communication layer that handles everything from API requests to local socket IPC with surgical precision.
ACME Without the Baggage
Managing SSL certificates is a core pillar of the ODAC experience. For a long time, we relied on acme-client to handle the heavy lifting of the RFC 8555 protocol. It worked, but it brought along a web of dependencies and a footprint that did not align with our vision.
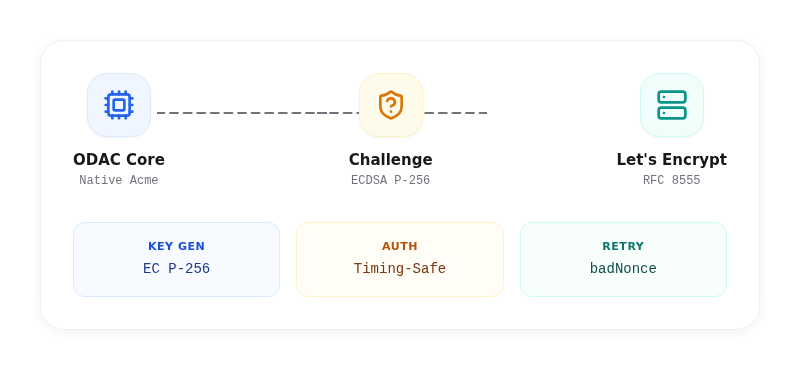
Our new native ACME client is a masterclass in minimalist engineering. We implemented the ACME protocol from scratch using Node.js built-in crypto and https modules.
But we did not stop at just replicating functionality. We upgraded the entire stack to use EC P-256 (ECDSA) for both account and domain keys. This provides security equivalent to RSA-3072 but with significantly faster handshakes and smaller payloads.
The new client also features integrated badNonce retry logic and timing-safe authentication comparisons, ensuring that your certificate renewals are as resilient as they are secure.
You can trigger certificate renewals with a single click from the app.odac.run dashboard, or if you prefer the terminal:
odac ssl renew --domain example.com
Securing the Mail Engine with Scrypt
Authentication is another area where we refused to compromise. We replaced the traditional bcrypt dependency with a native scrypt implementation for mail account security.
Native scrypt provides superior resistance to hardware-accelerated brute-force attacks compared to bcrypt. By using the Node.js built-in implementation, we removed yet another external binary dependency.
This shift allowed us to implement an adaptive hashing format that embeds cost parameters directly into the hash. As hardware improves, ODAC can transparently upgrade the security of your stored passwords upon login without requiring any manual intervention.
Why This Matters for the Enterprise
For our enterprise users, Zero-Bloat means more than just speed. It means a drastically reduced attack surface. By eliminating third-party supply chains from our core execution path, we have made ODAC significantly more resilient to the types of vulnerabilities that plague modern software.
It also means efficiency. The ODAC agent now operates with a significantly smaller memory footprint, allowing you to squeeze even more performance out of your hardware.
We are not just building another hosting platform. We are engineering the foundation for the next generation of the self-hosted cloud.
Welcome to the Zero-Bloat era.



