Hardening ODAC.JS with scrypt Hashing
In an era where GPU-accelerated brute-force attacks can cycle through millions of hashes per second, the standards of yesterday quickly become the vulnerabilities of tomorrow.
At ODAC.JS, we are committed to staying ahead of that curve, which is why we have officially migrated our core hashing engine from BCrypt to scrypt.
The Architecture of Resistance
Why the move to scrypt?
While BCrypt has served the Node.js ecosystem well for years, its primary weakness in the modern age is its reliance on CPU-bound work.
Specialized hardware like ASICs and FPGAs can parallelize BCrypt hashing with terrifying efficiency because the algorithm uses very little memory.
Enter scrypt.
By design, scrypt is a memory-hard algorithm.
It forces the attacker to dedicate significant amounts of RAM to each individual hashing attempt.
This architectural choice makes the cost of building specialized hardware for brute-forcing scrypt hashes exponentially higher, effectively leveling the playing field against even the most well-funded adversaries.
Seamless Developer Experience
In ODAC.JS, we believe that enterprise-grade security should not come at the cost of developer velocity.
The migration to scrypt is handled transparently within the ODAC.VAR utility.
When you call the .hash() method, the framework automatically handles the heavy lifting:
- Entropy Generation: A cryptographically secure 16-byte random salt is generated for every hash.
- Key Derivation: A high-entropy 64-byte key is derived using the scrypt algorithm.
- Safe Storage: The result is formatted as a self-describing string (
$scrypt$salt$hash) that is ready for database storage. - Timing-Safe Verification: Validation is performed using constant-time comparisons to prevent side-channel attacks.
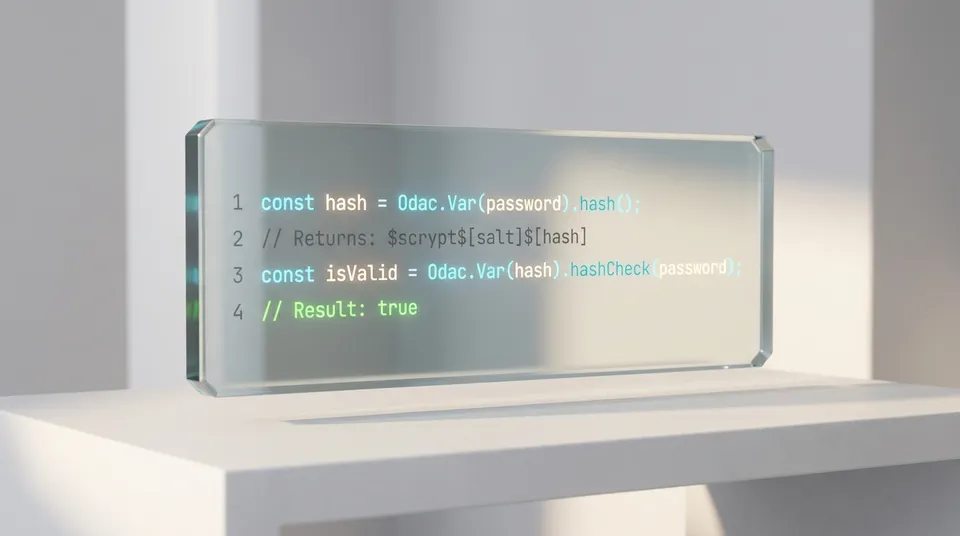
Show Me The Code
Implementing the new hashing standard requires exactly zero changes to your existing ODAC.JS workflow.
The ODAC.VAR API remains as clean and chainable as ever.
// Hashing a user's password during registration
const password = Odac.Request.post('password');
const secureHash = Odac.Var(password).hash();
// The result is an enterprise-grade scrypt hash
// Format: $scrypt$66063e...$a1b2c3...
await Odac.DB.users.insert({
email: Odac.Request.post('email'),
password: secureHash
});
Verifying the password during a login attempt is equally straightforward.
The framework detects the hashing algorithm automatically and applies the correct verification logic.
// Verifying a password during login
const user = await Odac.DB.users.where('email', email).first();
const isValid = Odac.Var(user.password).hashCheck(inputPassword);
if (isValid) {
await Odac.Auth.login(user.id);
return Odac.direct('/dashboard');
}
Pragmatic Backward Compatibility
We understand that enterprise applications cannot always migrate their entire user base overnight.
While all new hashes generated by the ODAC.AUTH and ODAC.VAR layers will use the scrypt algorithm by default, ODAC.JS maintains a pragmatic approach to backward compatibility.
The framework continues to support legacy MD5 and BCrypt hashes for verification purposes.
This allows you to upgrade your security posture today without locking out users who haven't updated their credentials since the migration.
As users log in, you can easily implement a "re-hash on login" pattern to migrate your entire database to scrypt over time.
Security as a Core Value
The move to scrypt is more than just a library update; it is a reflection of the ODAC.JS philosophy.
We prioritize the Why over the What, ensuring that every architectural decision we make contributes to a more resilient, performant, and secure Node.js ecosystem.
By making memory-hard hashing the default, we ensure that every application built on ODAC.JS is fortified against the hardware-accelerated threats of the future.



